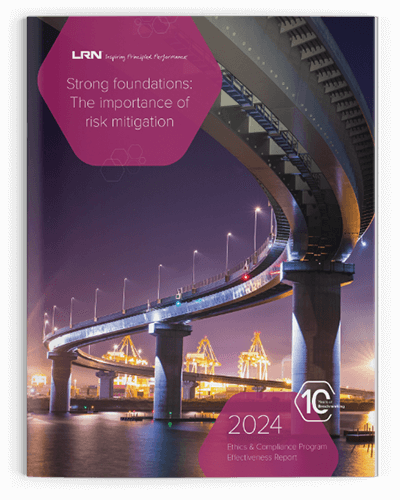
10 Years of Insight: The 2024 E&C Program Effectiveness Report
The 2024 Ethics & Compliance Program Effectiveness Report validates a central lesson from over 10 years of primary research—values-based programs are not only the most effective, but also correlate strongly with reduced risk and better business outcomes.
As new risks increase in severity and frequency around the world, we have focused our industry-leading analysis to provide the E&C community with a global view with specific and actionable insights.
500 +
TRAINING LESSONS
70 +
LANGUAGES
30000000 +
INSPIRED LEARNERS EACH YEAR
Now available.
Catalyst Reveal leverages learner outcomes and insights, AI, and industry benchmarks to provide real-time analytics and visibility into performance. Reduce organizational risk and build a business case for E&C innovation.

When AIB realized its “customer first” culture was starting to erode, they tapped LRN to develop custom training that would energize employees and re-instill their confidence in putting people at the center of their work.
Learn how Corteva and LRN put culture, ethics, and compliance in the palms of employees’ hands with a mobile app that was accessible to the entire global team—from those working at company headquarters to those working, literally, out in the field.
How can ethical culture enhance performance, reputation, and differentiation? LRN worked with Promigas, one of Latin America’s energy leaders, to answer that question—and helped them outperform industry benchmarks by more than 40% along the way.
Give a great presentation with the E&C KPI slide deck.
Presenting the progress and plans for your E&C program to stakeholders doesn’t have to be a daunting task. Use this PowerPoint template to wow your stakeholders, save yourself time, and get that all important executive buy-in.
Learning that connects and encourages empathy.
Effective E&C programs require education that resonates with your learners. Through inventive combinations of technology and content, we’ll design experiences that help your people think and act ethically no matter where they are. Our courses cover a wide variety of learning formats and topic areas, ensuring your curriculum reflects your brand, engages your learners, and gives your organization the means to outbehave and outperform.

Saas solutions to scale your program’s effectiveness.
Our inventive solutions deliver streamlined E&C program insight and management. From driving completions to measuring efficacy to instilling ethics into company culture, you’ll have everything you need to advance your program and ensure your learners can access essential information anytime, anywhere.